Artificial Intelligence is actively redefining innovation and driving large-scale transformation across every sector.
AI connectivity is the essential link between AI solutions and the data they need to perform at their absolute peak.
We bring efficiency to your AI projects by integrating and orchestrating with internal systems or third-party platforms.
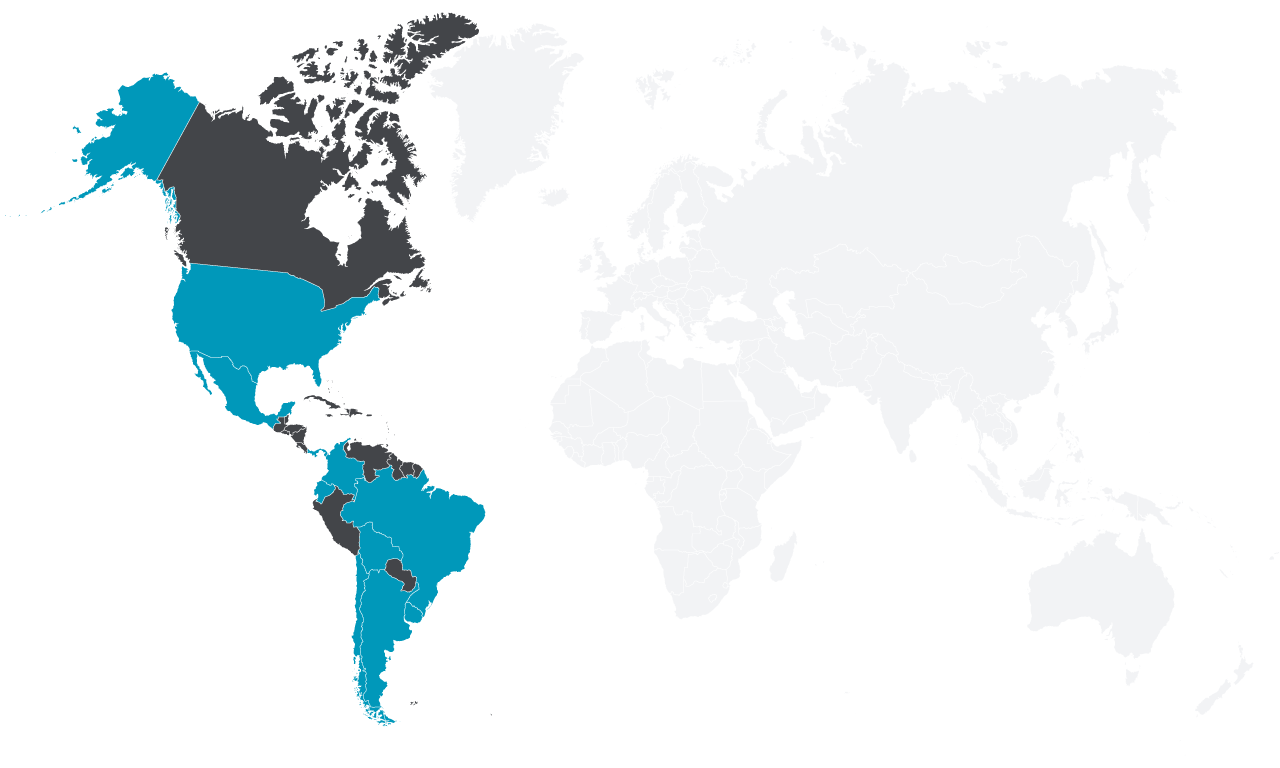
Driving the Agentic AI revolution in the Americas with our partners and clients
Corporate projects implemented in more than 10 countries in the region:
Uruguay, Brazil, Chile, Bolivia, Argentina, Ecuador, Colombia, Panama, Mexico & USA.
4
Offices
Uruguay, Brazil, Chile & USA
4
Solution Partners
3
Associations with International Consultancies